Future Technologies
EDGE TO EDGE COMMUNICATION – The majority of modern devices communicate to a central system and as new technologies push Artificial Intelligence to the edge, these devices can communicate with each other, enabling capabilities such as automatic tracking of people and vehicles in a closed, multi-camera CCTV system.
DEEP LEARNING ENGINES – Technology is now capable of learning and evolving automatically. An example of this is:
A person badges their access control card every day around 9am and exits around 5pm, then on one occasion they enter the building at 11pm, this anomaly is automatically raised as an alert for personnel to investigate.
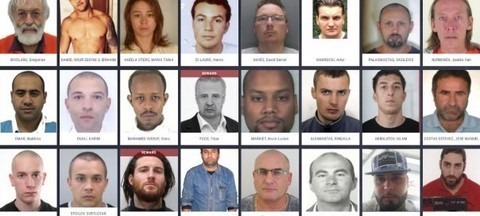
Facial Recognition
Facial recognition is used daily when you pass through an international border, open your computer or phone or log into a building’s visitor management system. Quality facial recognition systems are accurate, even if people lose or gain weight, or even wear a mask. Facial recognition is an excellent dual authentication option for access control systems.
Applications include:
- Dual authentication
- Access control
- Fast access control
- Identifying banned or high-risk individuals
- VIP management
- Locating lost children or people of interest/importance
- Customer service
- Checking queues at entry points
Brassets Group has extensive experience in the deployment of high-security facial recognition systems and integration into existing subsystems.
Intelligent Analytics
When designed and implemented correctly, video & audio analytics identify security and safety incidents automatically, alerting security or management staff immediately.
These incidents can include, but are not limited to:
- Unattended baggage or objects
- People running from a hazard
- Gunshots, explosions or people screaming
- Unauthorised entry / intrusion
- Queue lengths exceeding an acceptable length
- Unauthorised people/vehicles in a restricted area
- People not wearing high vis clothing in a construction area
- Slip and fall detection
Call Brassets Group to identify how AI and Analytics can improve business productivity, safety and security.

Our scale and experience improve productivity and culture outcomes
Our Security Management experts have compiled further information about our specialist services and accreditations for download here
Download Capability Statement
Security Capability Statement Download Form
Clinical Services Report Form